Are you seeking the best penetration testing tool for your needs? We have you covered.
Penetration testing tools are software applications used to check for network security threats.
Each application on this list provides unique benefits. Easy comparison helps you determine whether the software is the right choice for your business. Let’s dive in and discover the latest security software options on the market.
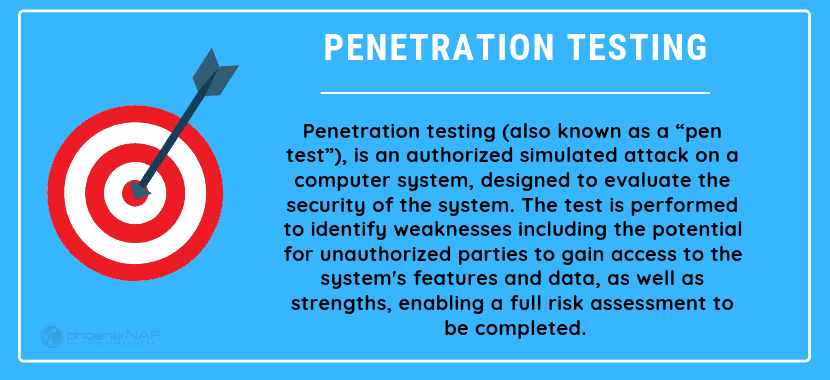
What Is Penetration Testing?
Penetration testing, also known as pen testing, means computer securities experts use to detect and take advantage of security vulnerabilities in a computer application. These experts, who are also known as white-hat hackers or ethical hackers, facilitate this by simulating real-world attacks by criminal hackers known as black-hat hackers.
In effect, conducting penetration testing is similar to hiring security consultants to attempt a security attack of a secure facility to find out how real criminals might do it. The results are used by organizations to make their applications more secure.
How Penetration Tests Work
First, penetration testers must learn about the computer systems they will be attempting to breach. Then, they typically use a set of software tools to find vulnerabilities. Penetration testing may also involve social engineering hacking threats. Testers will try to gain access to a system by tricking a member of an organization into providing access.
Penetration testers provide the results of their tests to the organization, which are then responsible for implementing changes that either resolve or mitigate the vulnerabilities.
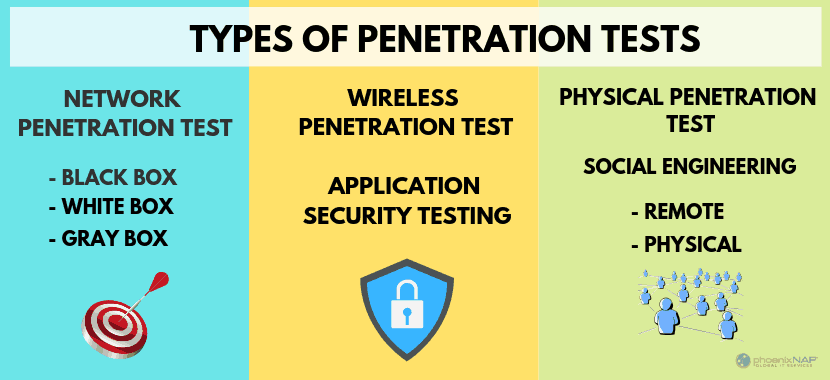
Types of Penetration Tests
Penetration testing can consist of one or more of the following types of tests:
White Box Tests
A white box test is one in which organizations provide the penetration testers with a variety of security information relating to their systems, to help them better find vulnerabilities.
Blind Tests
A blind test, known as a black-box test, organizations provide penetration testers with no security information about the system being penetrated. The goal is to expose vulnerabilities that would not be detected otherwise.
Double-Blind Tests
A double-blind test, which is also known as a covert test, is one in which not only do organizations not provide penetration testers with security information. They also do not inform their own computer security teams of the tests. Such tests are typically highly controlled by those managing them.
External Tests
An external test is one in which penetration testers attempt to find vulnerabilities remotely. Because of the nature of these types of tests, they are performed on external-facing applications such as websites.
Internal Tests
An internal test is one in which the penetration testing takes place within an organization’s premises. These tests typically focus on security vulnerabilities that someone working from within an organization could take advantage of.
Top Penetration Testing Software & Tools
1. Netsparker
Netsparker Security Scanner is a popular automatic web application for penetration testing. The software can identify everything from cross-site scripting to SQL injection. Developers can use this tool on websites, web services, and web applications.
The system is powerful enough to scan anything between 500 and 1000 web applications at the same time. You will be able to customize your security scan with attack options, authentication, and URL rewrite rules. Netsparker automatically takes advantage of weak spots in a read-only way. Proof of exploitation is produced. The impact of vulnerabilities is instantly viewable.
Benefits:
- Scan 1000+ web applications in less than a day!
- Add multiple team members for collaboration and easy shareability of findings.
- Automatic scanning ensures a limited set up is necessary.
- Searches for exploitable SQL and XSS vulnerabilities in web applications.
- Legal web application and regulatory compliance reports.
- Proof-based scanning Technology guarantees accurate detection.
2. Wireshark
Once known as Ethereal 0.2.0, Wireshark is an award-winning network analyzer with 600 authors. With this software, you can quickly capture and interpret network packets. The tool is open-source and available for various systems, including Windows, Solaris, FreeBSD, and Linux.
Benefits:
- Provides both offline analysis and live-capture options.
- Capturing data packets allows you to explore various traits, including source and destination protocol.
- It offers the ability to investigate the smallest details for activities throughout a network.
- Optional adding of coloring rules to the pack for rapid, intuitive analysis.
3. Metasploit
Metasploit is the most used penetration testing automation framework in the world. Metasploit helps professional teams verify and manage security assessments, improves awareness, and arms and empowers defenders to stay a step ahead in the game.
It is useful for checking security and pinpointing flaws, setting up a defense. An Open source software, this tool will allow a network administrator to break in and identify fatal weak points. Beginner hackers use this tool to build their skills. The tool provides a way to replicates websites for social engineers.
Benefits:
- Easy to use with GUI clickable interface and command line.
- Manual brute-forcing, payloads to evade leading solutions, spear phishing, and awareness, an app for testing OWASP vulnerabilities.
- Collects testing data for over 1,500 exploits.
- MetaModules for network segmentation tests.
- You can use this to explore older vulnerabilities within your infrastructure.
- Available on Mac Os X, Windows and Linux.
- Can be used on servers, networks, and applications.
4. BeEF
This is a pen testing tool and is best suited for checking a web browser. Adapted for combating web-borne attacks and could benefit mobile clients. BeEF stands for Browser Exploitation Framework and uses GitHub to locate issues. BeEF is designed to explore weaknesses beyond the client system and network perimeter. Instead, the framework will look at exploitability within the context of just one source, the web browser.
Benefits:
- You can use client-side attack vectors to check security posture.
- Connects with more than one web browser and then launch directed command modules.
5. John The Ripper Password Cracker
Passwords are one of the most prominent vulnerabilities. Attackers may use passwords to steal credentials and enter sensitive systems. John the Ripper is the essential tool for password cracking and provides a range of systems for this purpose. The pen testing tool is a free open source software.
Benefits:
- Automatically identifies different password hashes.
- Discovers password weaknesses within databases.
- Pro version is available for Linux, Mac OS X, Hash Suite, Hash Suite Droid.
- Includes a customizable cracker.
- Allows users to explore documentation online. This includes a summary of changes between separate versions.
6. Aircrack
Aircrack NG is designed for cracking flaws within wireless connections by capturing data packets for an effective protocol in exporting through text files for analysis. While the software seemed abandoned in 2010, Aircrack was updated again in 2019.
This tool is supported on various OS and platforms with support for WEP dictionary attacks. It offers an improved tracking speed compared to most other penetration tools and supports multiple cards and drivers. After capturing the WPA handshake, the suite is capable of using a password dictionary and statistical techniques to break into WEP.
Benefits:
- Works with Linux, Windows, OS X, FreeBSD, NetBSD, OpenBSD, and Solaris.
- You can use this tool to capture packets and export data.
- It is designed for testing wifi devices as well as driver capabilities.
- Focuses on different areas of security, such as attacking, monitoring, testing, and cracking.
- In terms of attacking, you can perform de-authentication, establish fake access points, and perform replay attacks.
7. Acunetix Scanner
Acutenix is an automated testing tool you can use to complete a penetration test. The tool is capable of auditing complicated management reports and issues with compliance. The software can handle a range of network vulnerabilities. Acunetix is even capable of including out-of-band vulnerabilities.
The advanced tool integrates with the highly enjoyed Issue Trackers and WAFs. With a high-detection rate, Acunetix is one of the industry’s advanced Cross-site scripting and SQLi testing, which includes sophisticated advanced detection of XSS.
Benefits:
- The tool covers over 4500 weaknesses, including SQL injection as well as XSS.
- The Login Sequence Recorder is easy-to-implement and scans password-protected areas.
- The AcuSensor Technology, Manual Penetration tools, and Built-in Vulnerability Management streamline black and white box testing to enhance and enable remediation.
- Can crawl hundreds of thousands of web pages without delay.
- Ability to run locally or through a cloud solution.
8. Burp Suite Pen Tester
There are two different versions of the Burp Suite for developers. The free version provides the necessary and essential tools needed for scanning activities. Or, you can opt for the second version if you need advanced penetration testing. This tool is ideal for checking web-based applications. There are tools to map the tack surface and analyze requests between a browser and destination servers. The framework uses Web Penetration Testing on the Java platform and is an industry-standard tool used by the majority of information security professionals.
Benefits:
- Capable of automatically crawling web-based applications.
- Available on Windows, OS X, Linux, and Windows.
9. Ettercap
The Ettercap suite is designed to prevent man in the middle attacks. Using this application, you will be able to build the packets you want and perform specific tasks. The software can send invalid frames and complete techniques which are more difficult through other options.
Benefits:
- This tool is ideal for deep packet sniffing as well as monitoring and testing LAN.
- Ettercap supports active and passive dissection of protections.
- You can complete content filtering on the fly.
- The tool also provides settings for both network and host analysis.
10. W3af
W3af web application attack and audit frameworks are focused on finding and exploiting vulnerabilities in all web applications. Three types of plugins are provided for attack, audit, and discovery. The software then passes these on to the audit tool to check for flaws in the security.
Benefits:
- Easy to use for amateurs and powerful enough for developers.
- It can complete automated HTTP request generation and raw HTTP requests.
- Capability to be configured to run as a MITM proxy.
11. Nessus
Nessus has been used as a security penetration testing tool for twenty years. 27,000 companies utilize the application worldwide. The software is one of the most powerful testing tools on the market with over 45,000 CEs and 100,000 plugins. Ideally suited for scanning IP addresses, websites and completing sensitive data searches. You will be able to use this to locate ‘weak spots’ in your systems.
The tool is straightforward to use and offers accurate scanning and at the click of a button, providing an overview of your network’s vulnerabilities. The pen test application scans for open ports, weak passwords, and misconfiguration errors.
Benefits:
- Ideal for locating and identify missing patches as well as malware.
- The system only has .32 defects per every 1 million scans.
- You can create customized reports, including types of vulnerabilities by plugin or host.
- In addition to web application, mobile scanning, and cloud environment, the tool offers priority remediation.
12. Kali Linux
Kali Linux advanced penetration testing software is a Linux distribution used for penetration testing. Many experts believe this is the best tool for both injecting and password snipping. However, you will need skills in both TCP/IP protocol to gain the most benefit. An open-source project, Kali Linux, provides tool listings, version tracking, and meta-packages.
Benefits:
- With 64 bit support, you can use this tool for brute force password cracking.
- Kali uses a live image loaded into the RAM to test the security skills of ethical hackers.
- Kali has over 600 ethical hacking tools.
- Various security tools for vulnerability analysis, web applications, information gathering, wireless attacks, reverse engineering, password cracking, forensic tools, web applications, spoofing, sniffing, exploitation tools, and hardware hacking are available.
- Easy integration with other penetration testing tools, including Wireshark and Metasploit.
- The BackTrack provides tools for WLAN and LAN vulnerability assessment scanning, digital forensics, and sniffing.
Check out our comparison of Kali Linux and Ubuntu.
13. SQLmap
SQLmap is an SQL injection takeover tool for databases. Supported database platforms include MySQL, SQLite, Sybase, DB2, Access, MSSQL, PostgreSQL. SQLmap is open-source and automates the process of exploiting database servers and SQL injection vulnerabilities.
Benefits:
- Detects and maps vulnerabilities.
- Provides support for all injection methods: Union, Time, Stack, Error, Boolean.
- Runs software at the command line and can be downloaded for Linux, Mac OS, and Windows systems
14. (SET) Social Engineer Toolkit
Social engineering is the primary focus of the toolkit. Despite the aim and focus, human beings are not the target of vulnerability scanners.
Benefits:
- It has been featured at top cybersecurity conferences, including ShmooCon, Defcon, DerbyCon and is an industry-standard for penetration tests.
- SET has been downloaded over 2 million times.
- An open-source testing framework designed for social engineering detection.
15. Zed Attack Proxy
OWASP ZAP (Zed Attack Proxy) is part of the free OWASP community. It is ideal for developers and testers that are new to penetration testing. The project started in 2010 and is improved daily. ZAP runs in a cross-platform environment creating a proxy between the client and your website.
Benefits:
- 4 modes available with customizable options.
- To install ZAP, JAVA 8+ is required on your Windows or Linux system.
- The help section is comprehensive with a Getting Started (PDF), Tutorial, User Guide, User Groups, and StackOverflow.
- Users can learn all about Zap development through Source Code, Wiki, Developer Group, Crowdin, OpenHub, and BountySource.
16. Wapiti
Wapiti is an application security tool that allows black box testing. Black box testing checks web applications for potential liabilities. During the black box testing process, web pages are scanned, and the testing data is injected to check for any lapses in security.
- Experts will find ease-of-usability with the command-line application.
- Wapiti identifies vulnerabilities in file disclosure, XSS Injection, Database injection, XXE injection, Command Execution detection, and easily bypassed compromised .htaccess configurations.
17. Cain & Abel
Cain & Abel is ideal for procurement of network keys and passwords through penetration. The tool makes use of network sniffing to find susceptibilities.
- The Windows-based software can recover passwords using network sniffers, cryptanalysis attacks, and brute force.
- Excellent for recovery of lost passwords.
Get Started with Penetration Testing Software
Finding the right pen testing software doesn’t have to be overwhelming. The tools listed above represent some of the best options for developers.
Remember one of the best techniques to defend your IT structure is to use penetration testing proactively. Assess your IT security by looking for and discovering issues before potential attackers do.