Man-in-the-middle (MITM) attacks are a growing threat to online communication. In this type of cyber attack, hackers secretly intercept and manipulate data exchanged between victims. The covert nature of MITM attacks makes them exceptionally difficult to detect, potentially leaving individuals and organizations vulnerable without their knowledge.
Understanding the different types, methods, and stages of MITM attacks is crucial for effective protection.
This article provides a comprehensive overview of man-in-the-middle attacks, cataloging the hackers' methods and offering actionable strategies to mitigate the risks.
What is a Man-in-the-Middle Attack?
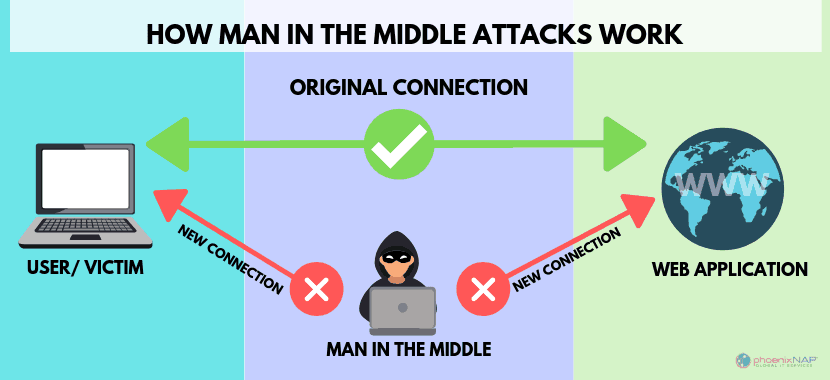
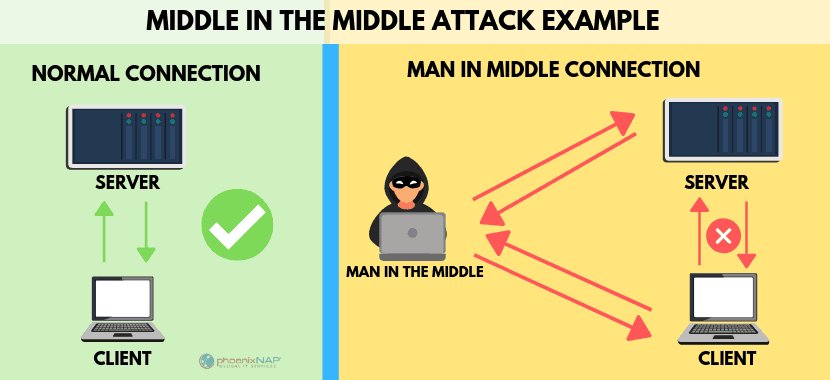
MITM attacks involve attackers secretly intercepting and potentially altering communication between two parties who believe they are communicating directly. The aim of these attacks is to steal sensitive information or inject malware.
Here are the key characteristics of MITM attacks:
- Real-time interception. Data is intercepted, altered, or stolen as it is transmitted, making detection and response difficult.
- Exploiting vulnerabilities. Attackers leverage weaknesses in network security to impersonate legitimate participants.
- Separate information streams. The attacker controls two independent communication channels, one with each victim, all the time appearing as the other party to each.

How Does a Man-in-the-Middle Attack Work?
A man-in-the-middle attack has six distinct stages. Here's a detailed look at each stage.
1. Interception
The initial step of an MITM attack involves the attacker establishing a position between the two communicating parties. The goal is to silently intercept communication without raising suspicion from either participant. Attackers achieve this infiltration through various means.
One common method is by utilizing ARP spoofing within a local network. By associating their hardware address with the IP address of the victim’s device, the attacker can enable all data to be rerouted through their system first. This tactic grants them access to the information exchanged between the legitimate participants.
2. Decryption
After successfully intercepting the communication, the attacker may need to decrypt the data if it is encrypted. Many communications use encryption protocols like HTTPS to secure data in transit. Attackers use techniques such as SSL stripping to downgrade an encrypted connection to an unencrypted one, enabling them to view and modify the transmitted data.
Hackers who cannot bypass the encryption might exploit vulnerabilities in the encryption protocol or use phishing and social engineering to acquire encryption keys.
3. Eavesdropping and Data Harvesting
With the communication intercepted (and possibly decrypted), the attacker silently monitors and captures the transmitted data. This stage is critical for the attacker to gather sensitive and confidential information being communicated between the parties.
The success of this stage depends on the attacker's ability to remain undetected and gather data over time.
4. Data Capture and Manipulation
In addition to eavesdropping, the attacker can alter the data before it reaches its intended recipient. This alteration could involve:
- Injecting malicious code.
- Altering transaction details in financial communications.
- Sending fraudulent responses.
This manipulation serves various purposes, including fraud, spreading malware and ransomware, or furthering the attacker's access to secure systems via lateral movement.
5. Session Hijacking
Once the attacker has gathered enough information, they may hijack an active session. Using stolen session tokens or cookies, the attacker impersonates a legitimate user, gaining unauthorized access.
This stage is particularly dangerous because it allows the attacker to perform actions on behalf of the user, such as making transactions, altering account details, or accessing restricted information.
6. Maintaining Access
The final stage of many MITM attacks involves establishing mechanisms to ensure continued access to the target's system or network. The attacker may install backdoors and rootkits or use the compromised credentials for future attacks.
Maintaining access allows the attacker to continuously monitor and exploit the target, gathering more data or causing further damage over time. Exceptionally skilled hackers can remain hidden for months or even years.
Types of Man in the Middle Attack
MITM attacks can take various forms, exploiting different vulnerabilities in communication systems. Unfortunately, new techniques for MITM attacks are constantly emerging.
Here is a comprehensive list of MITM attack types with brief explanations.
1. ARP Spoofing
ARP (Address Resolution Protocol) Spoofing targets the resolution process between IP and MAC (Media Access Control) addresses in a local area network (LAN). Attackers send fake ARP messages to associate their MAC address with the IP address of another host. As a result, traffic meant for that IP address is mistakenly sent to the attacker, allowing them to intercept, inspect, or modify data before forwarding it to the intended recipient.
2. IP Spoofing
In an IP spoofing attack, the attacker deceives a system by emulating the IP address of a trusted host. This manipulation makes the receiving system accept the incoming packet, believing it is from a known, secure source. The attacker can then intercept, send, or receive data intended for the legitimate host without detection.
3. DNS Spoofing
DNS (Domain Name System) Spoofing involves corrupting the domain name system resolution process to redirect traffic from legitimate websites to fraudulent ones controlled by the attacker.
By poisoning the DNS cache, attackers replace the IP address of a legitimate site with that of a malicious one. Users attempting to access the legitimate site are unknowingly redirected to the attacker's site, where they may disclose sensitive information.
4. SSL Stripping
SSL (Secure Sockets Layer) stripping attacks target the transition from non-secure HTTP connections to secure HTTPS connections. HTTPS is widely recognized as a symbol of website security because it protects data from being intercepted by encrypting it during transmission between a user's web browser and the website.
Attackers intercept the initial request to transition to HTTPS and force the connection to remain over HTTP. Stripping the encryption allows the attacker to view and modify the unsecured traffic between the user and the website.
5. HTTPS Spoofing
HTTPS spoofing attacks involve creating a fraudulent website that visually mimics a trusted one, for example, a bank, social media platform, or retail site. The fake website's URL closely resembles the legitimate site's, using minor discrepancies like typos or different domain suffixes (e.g., .net instead of .com), and is even secured with HTTPS through a technically valid but illegitimate SSL/TLS certificate.
Unsuspecting users, deceived by the familiar appearance and the presence of HTTPS, enter sensitive information on the spoofed site. This information is then directly transmitted to the attacker.
6. Wi-Fi Eavesdropping
Wi-Fi Eavesdropping occurs when attackers set up rogue access points or compromise legitimate ones to spy on the data transmitted over the network. Users connecting to such networks unknowingly expose their data to the attacker.
7. Session Hijacking (Cookie Hijacking)
During session hijacking, attackers intercept and steal session cookies, which are used to authenticate website users. By obtaining these cookies, attackers can impersonate the victim and gain unauthorized access to their accounts and sessions, bypassing login mechanisms.
8. Man-in-the-Browser Attack
Man-in-the-Browser attacks involve malware that infects a web browser. This malware intercepts and manipulates web transactions as they occur without the user or web application noticing. The malware can alter transaction content, insert additional transactions, or steal information entered by the user in the browser.
9. Email Hijacking
Email Hijacking involves gaining unauthorized access to or intercepting email communications. Attackers compromise email accounts to send and receive messages without the owner's consent or intercept emails in transit. This tactic allows them to access sensitive information, spread malware, and conduct spear phishing attacks.
10. IM Snooping
IM (Instant Messaging) snooping attacks focus on intercepting instant messaging communications. Attackers exploit IM software or network vulnerabilities to capture messages with the goal of gathering sensitive information or spreading malware.
11. VoIP Eavesdropping
VoIP eavesdropping involves intercepting Voice over Internet Protocol (VoIP) calls through vulnerabilities in the VoIP software or network security. If successful, attackers can listen to private conversations, record them, and use the data transmitted during the call for malicious purposes.
12. Evil Twin Wi-Fi Attacks
In an Evil Twin Wi-Fi attack, the attacker sets up a malicious Wi-Fi network that mimics a legitimate one, often in public places. Users are tricked into connecting to this network instead of the legitimate one. Once connected, the attacker can monitor and capture all data transmitted by the user.
Man in the Middle Attack Example
The following MITM attacks were widely discussed in the cybersecurity community or reported in the media. These examples illustrate the diversity of MITM attacks across different sectors and their impact.
Kazakhstan Man-in-the-Middle Attack
The Kazakhstan Man-in-the-Middle Attack refers to a series of cybersecurity incidents targeting internet users within Kazakhstan. In 2015, the Kazakh government attempted to intercept HTTPS traffic by requiring citizens to install a government-issued root certificate on their devices. This certificate would allow the government to decrypt, view, and modify any encrypted internet traffic between users and websites, effectively enabling widespread surveillance and censorship.
However, the Kazakh government faced significant backlash from organizations and browser makers like Mozilla and Google. They argued that such actions compromised user security and privacy, so the plan was temporarily halted.
However, in July 2019, the government renewed its efforts, mandating that all internet users in the country's capital install the government-issued certificate. This action prompted immediate responses from browser and operating system developers, including Mozilla, Google, and Apple, who updated their software to reject the Kazakh certificate.
NSA Impersonation of Google
In a series of reports emerging around 2013, it was revealed that the National Security Agency (NSA) of the United States had disguised itself as Google to conduct surveillance and gather data.
This strategy involved man-in-the-middle attacks, where the NSA intercepted users' internet communications by masquerading as the tech giant. By creating fake Google servers, the NSA could trick users' computers into thinking they were securely communicating with Google, allowing the agency to decrypt and analyze their internet traffic.
This operation was part of a broader NSA surveillance program, details of which were leaked by Edward Snowden, a former NSA contractor. The incident led to widespread scrutiny of the NSA's practices and calls for more transparency in government surveillance activities.
Superfish Malware
Superfish was a controversial adware program that became widely known for being pre-installed on some Lenovo laptops sold between 2014 and 2015. The software was designed to analyze users' internet browsing images and inject third-party advertisements into web pages, purportedly to help users find and compare similar products online. However, the method used to display ads compromised user security.
The core issue with Superfish was that it installed a self-signed root certificate authority (CA), which allowed it to intercept encrypted HTTPS traffic. This capability enabled the software to conduct an MITM attack on the user's internet connection, decrypting and re-encrypting web traffic to inject ads into secure websites without triggering browser security warnings.
This practice exposed users to significant security vulnerabilities, as any attacker with access to the Superfish certificate's private key could intercept, decrypt, and modify the user's encrypted web traffic. The discovery of Superfish led to a public outcry that forced Lenovo to remove the software from its devices and issue a tool to uninstall it and remove the rogue certificate from affected systems.

Man in the Middle Attack Prevention
Defending against MITM attacks involves a combination of technological solutions, security protocols, and user awareness. Here are strategies to prevent MITM attacks.
Use of Encryption
Encryption ensures that even if data is intercepted, it remains unreadable and secure from unauthorized access.
- Implement HTTPS. Websites that use the HTTPS protocol encrypt data in transit, making it difficult for attackers to decipher intercepted communications.
- Use end-to-end encryption in messaging. Only use messaging platforms that offer end-to-end encryption. Encrypting data at rest, in use, and in transit ensures that only legitimate users can read the messages.
- Encrypt sensitive data. Encrypt sensitive data such as financial information, personal identification data, and login credentials before transmission.
Secure Networking
Securing your network infrastructure and the data flowing through it reduces the risk of MITM attacks.
- Secure Wi-Fi networks. Use strong passwords for Wi-Fi networks and enable WPA3 encryption to protect against unauthorized access and eavesdropping.
- Avoid public Wi-Fi for sensitive transactions. Public Wi-Fi networks are prime targets for MITM attacks. Avoid conducting sensitive transactions, such as banking or shopping, on public Wi-Fi. Use a reputable Virtual Private Network (VPN) to encrypt your data on public networks.
- Implement VPNs for remote access. A VPN creates a secure, encrypted tunnel for data transmission between a user's device and the network, protecting data from interceptors.
Authentication and Verification
Proper authentication and verification mechanisms ensure that communicators are who they claim to be, preventing attackers from inserting themselves into the process.
- Digital certificates and public key infrastructure (PKI). Digital certificates issued by trusted Certificate Authorities (CAs) verify the authenticity of websites and services. PKI provides a framework for encryption and digital signature services.
- Multi-factor authentication (MFA). Implement MFA to add an extra layer of security. It ensures that even if login credentials are compromised, unauthorized access is still blocked.
Regular Updates and Patching
Updating software and systems is crucial, as these updates include patches for known vulnerabilities.
- Update and patch regularly. Keep all systems, software, and applications updated with the latest security patches. Attackers often exploit known vulnerabilities that have been patched in newer software versions.
- Secure network devices. Ensure that network devices such as routers and switches are updated and properly configured to defend against attacks.
Awareness and Training
Educating users on the risks and signs of MITM attacks is vital in preventing them.
- Educate users. Conduct regular security awareness training to educate users about the risks of MITM attacks and the importance of cybersecurity best practices, such as verifying the authenticity of websites and being on the lookout for phishing attempts.
- Monitor for suspicious activity. Use network monitoring tools to detect unusual patterns or activities that could indicate an MITM attack, such as ARP spoofing or unexpected HTTPS downgrades.
Implement Network Security Measures
These technical security measures can stop MITM attacks in their tracks.
- Use intrusion detection systems (IDS) and intrusion prevention systems (IPS). These systems detect and prevent suspicious activities and attack patterns associated with MITM attempts.
- Deploy firewalls. Firewalls control incoming and outgoing network traffic based on an applied rule set, helping to prevent unauthorized access and data breaches.
Secure DNS Practices
Securing DNS queries and responses prevents attackers from redirecting users to malicious sites, a common tactic in MITM attacks.
- DNS security extensions (DNSSEC). Implement DNSSEC to protect against DNS spoofing by ensuring the authenticity and integrity of DNS responses.
- Use DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT). These protocols encrypt DNS queries, making it harder for attackers to manipulate DNS resolutions.
To keep your DNS infrastructure healthy, read our article on best practices for DNS security and performance.

Building Resilience against MITM
Modern organizations operate in a complex ecosystem with increased productivity and innovation but also heightened cybersecurity risks, particularly from MITM attacks. Business mobility, remote work, and widespread IoT adoption amplify vulnerability as attacks exploit unencrypted data.
Addressing these attacks requires a layered approach. Comprehensive encryption protocols are essential; however, they must be coupled with securing network infrastructure through advanced tools, regular assessments, and secure communication protocols.
Beyond technical measures, a cybersecurity culture is crucial. Employees are the first line of defense and need the knowledge and tools to recognize and respond to threats. Training, simulations, and clear guidelines for secure online behavior are essential components of a comprehensive IT security policy, which will protect your financial and digital assets.



