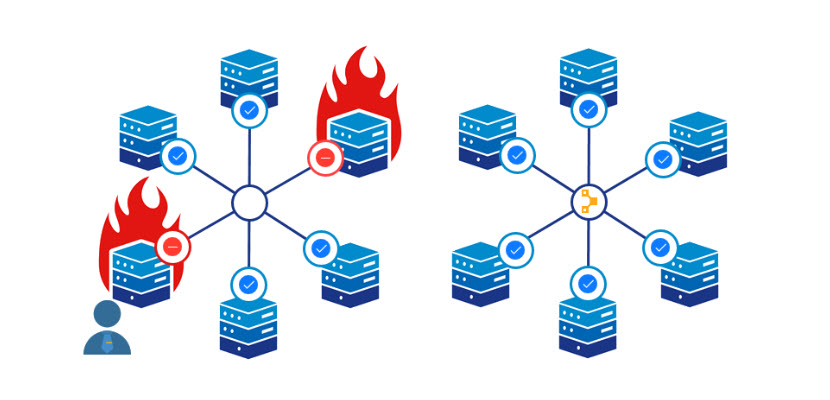
In DevOps, you want to automate as many tasks as possible. Manually configuring environments takes weeks with vast infrastructures. By the time everything is set up, you're putting out fires instead of implementing new effective solutions, such as Rancher servers.
Puppet helps automate manual tasks to quickly provision systems and deploy applications. Dynamic infrastructure management is at the core of Puppet.
This article explains what Puppet is, which problems it solves, and how to use Puppet to automate manual jobs as a DevOps team successfully.
What is Puppet?
Puppet is an IaC (Infrastructure as Code) tool for managing multiple servers. Written in Ruby (primarily), Puppet operates on multiple Unix-like systems and supports Windows too.
The software is highly mature, with the initial release being in 2005. Puppet comes as free, open-source software, and a proprietary version is also available for complex infrastructures.
What Is Puppet Used For?
Puppet automates server configuration management and deployment. The software enables pulling strings and managing states on multiple systems at once, and the approach reduces manual setup and management of servers individually.
Puppet defines the desired state for the system rather than how to get there. The configuration applies to various platforms and devices and maintains the state across the infrastructure. Overall, there’s less need for system administrators to put out fires, allowing the DevOps team to implement new and better server solutions.
phoenixNAP’s custom Puppet module on GitHub lets you manage CA Trust anchors within the ca-certificates framework. Manage and automate Bare Metal Cloud servers with Puppet easily.
Puppet Configuration Management
Automation scripts help handle repetitive tasks, such as installing and configuring servers. However, when working with an extensive infrastructure, automation scripts don't scale.
Configuration management provides a solution for extensive infrastructure configurations. The practices are considered the backbone of DevOps and allow for frequent and more reliable software releases in an established DevOps pipeline.
Server configuration management occurs thanks to the infrastructure-as-code approach. In the case of Puppet, the server management code is in Puppet code, which is similar to Ruby. The language is declarative and describes a model-based configuration.
How Does Puppet Work?
Puppet uses a client-server approach and consists of the following systems:
- The Puppet Master is a server with the Puppet Master daemon that manages crucial system information for all nodes using manifests.
- The Puppet Agents are nodes with Puppet installed on them with the Puppet Agent daemon running.
The sections below explain the essential Puppet elements and terminology, which help clarify how Puppet works.
Puppet Topology and Architecture
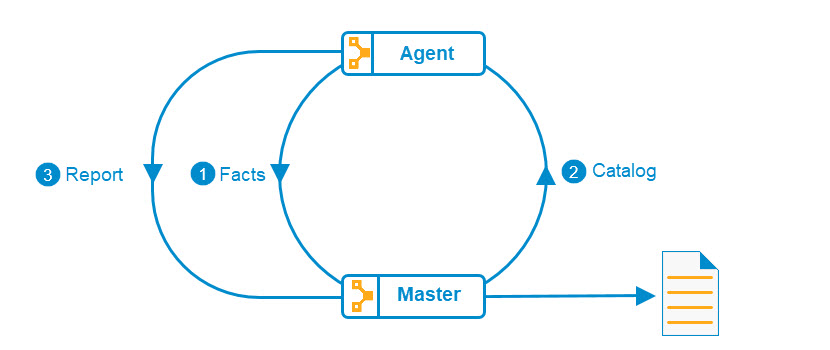
Puppet utilizes a client/server architecture consisting of the Puppet Master and Puppet Agents. Puppet Agents uses pull mode to poll the master and retrieve node-specific and site-specific configuration info.
The topology goes through the following steps:
- A node running a Puppet Agent daemon gathers all the information (facts) about itself, and the agent sends the facts to the Puppet Master.
- The Puppet Master uses the data to create a catalog on how the node should be configured and sends it back to the Puppet Agent.
- The Puppet Agent configures itself based on the catalog and reports back to the Puppet Master.
Puppet uses a utility called Facter to discover system information. The tool comes with the Puppet installation by default.
To install Puppet, follow our guides:
How to Install Puppet on Ubuntu 20.04
How to Install Puppet on MacOS
Puppet Master
The Puppet Master is a daemon running on a dedicated server. The Puppet Master is the information source and configuration authority as a server node. The master sends instructions to all agent nodes and oversees the system's configuration.
The Puppet Master is responsible for the following tasks:
- Creating a catalog for the agents.
- File transfers from a file server to agents.
- Accepting SSL certificates from agents.
- Storing configuration manifests.
Puppet uses identity access management through a dedicated user and group, providing security and exposing only the required information to agents. However, not all actions require elevated privileges.
Puppet Agents
The Puppet Agent is a Puppet daemon running on a system or node. Agents have certain privileges on the node to apply configuration catalogs pulled from the Puppet Master.
To receive communication permissions, an agent requests an SSL certificate during first contact with the master. The certificate is checked every time the agent asks the master for configuration updates before sending the information. A master also authenticates to the agents to ensure correct configuration info.
Puppet agents modify the system’s configuration and require root permissions to perform tasks.
Puppet Encryption and Communication Security
Puppet uses OpenSSL for communication and security. Based on SSL and TLS protocols, Puppet uses standard SSL/TLS encryption and SSL certificates for agent/master authentication and verification. Additionally, Puppet encrypts the traffic flow between the agents and servers using SSL/TLS using SHA-256 as the default hash.
Encryption methods in Puppet ensure the following:
- Master/agent authentication and verification.
- Preventing data breaches between master and agents.
The master generates its own CA certificate, private key, CRL (Certificate Revocation List), and a server certificate. The server certificate is sent to agents to enable SSL and TLS communication.
Advantages of Puppet and Why You Should Use It
Puppet is one of the longest-standing and most popular configuration management automation tools. Below are five advantages that give good reasons to start using Puppet.
1. Open source
Puppet is open source, which makes the technology extensible. Custom libraries and modules enrich individual projects to suit your use case.
Open source also comes with the benefit of having an active community. Plenty of discussions, forums, and experts are ready to help out and answer questions.
phoenixNAP supports the open-source community and gives back by maintaining public GitHub repositories with modules for automating server deployment and management.
2. Resource Abstraction
Configuration tasks are repetitive, and the same steps are often required on servers with different operating systems through platform-specific steps. Remembering all the commands is an impossible task.
Facter helps Puppet figure out the specifics and achieve abstraction. System-specific data and OS details are all familiar to Puppet thanks to Facter.
3. Idempotency
Redundant configurations are a complex issue when working with numerous servers, and Puppet aims to apply only those changes that affect the system. If the desired state of the infrastructure is achieved, Puppet doesn't run the commands. This Puppet feature is known as idempotency, which helps reduce redundancy and increase efficiency.
4. Cross-Platform
Puppet covers a wide range of platforms, which increases the number of servers in the configuration automation process. The tool works on Windows, OS X, Debian-based systems, Fedora, Gentoo, RHEL, and Solaris.
5. Flexible
The Puppet language includes a way to override instructions and create exceptions for different scenarios. Puppet also aids in scheduling specific maintenance actions periodically.
Conclusion
Puppet is a powerful tool for managing configurations and server tasks, and it's an excellent choice for stable servers that don't change dynamically or often.
To see how Puppet compares with other similar technologies, check out our comparison article on Terraform vs. Puppet.